Data security has become one of the most important concerns for businesses today. From financial transactions to personal information, organizations handle sensitive data that must be protected at all costs. With cyber threats increasing every year, relying only on basic security methods is no longer enough.
This is where HSM modules come into the picture. These advanced security devices are designed to protect sensitive data by managing encryption keys in a highly secure way. Businesses across industries are now using HSM modules to strengthen their data protection systems and reduce the risk of breaches.
In this blog, we will understand what HSM modules are, how they work, and why they are important for modern data encryption.
What Are HSM Modules?
HSM modules, also known as Hardware Security Modules, are physical devices used to secure and manage digital encryption keys. They are designed to perform cryptographic operations such as encryption, decryption, key generation, and digital signing in a safe environment.
Unlike software-based security tools, HSM modules operate in a dedicated hardware system that is isolated from regular networks. This makes them more secure and resistant to attacks.
Key Features of HSM Modules
- Tamper-resistant hardware design
- Secure generation and storage of encryption keys
- High-performance cryptographic processing
- Strong access control mechanisms
- Compliance with security standards
These features make HSM modules a reliable solution for protecting sensitive data.
Why Are HSM Modules Important for Data Encryption?
Encryption is a method used to convert readable data into an unreadable format to prevent unauthorized access. However, encryption is only effective if the keys used are properly protected.
HSM modules ensure that encryption keys are never exposed or misused. They provide a secure environment where all cryptographic operations take place.
Key Benefits
- Protect sensitive business data
- Prevent unauthorized access
- Ensure secure communication
- Support regulatory compliance
- Reduce risk of data breaches
This is why many businesses are now investing in HSM modules for better data security.
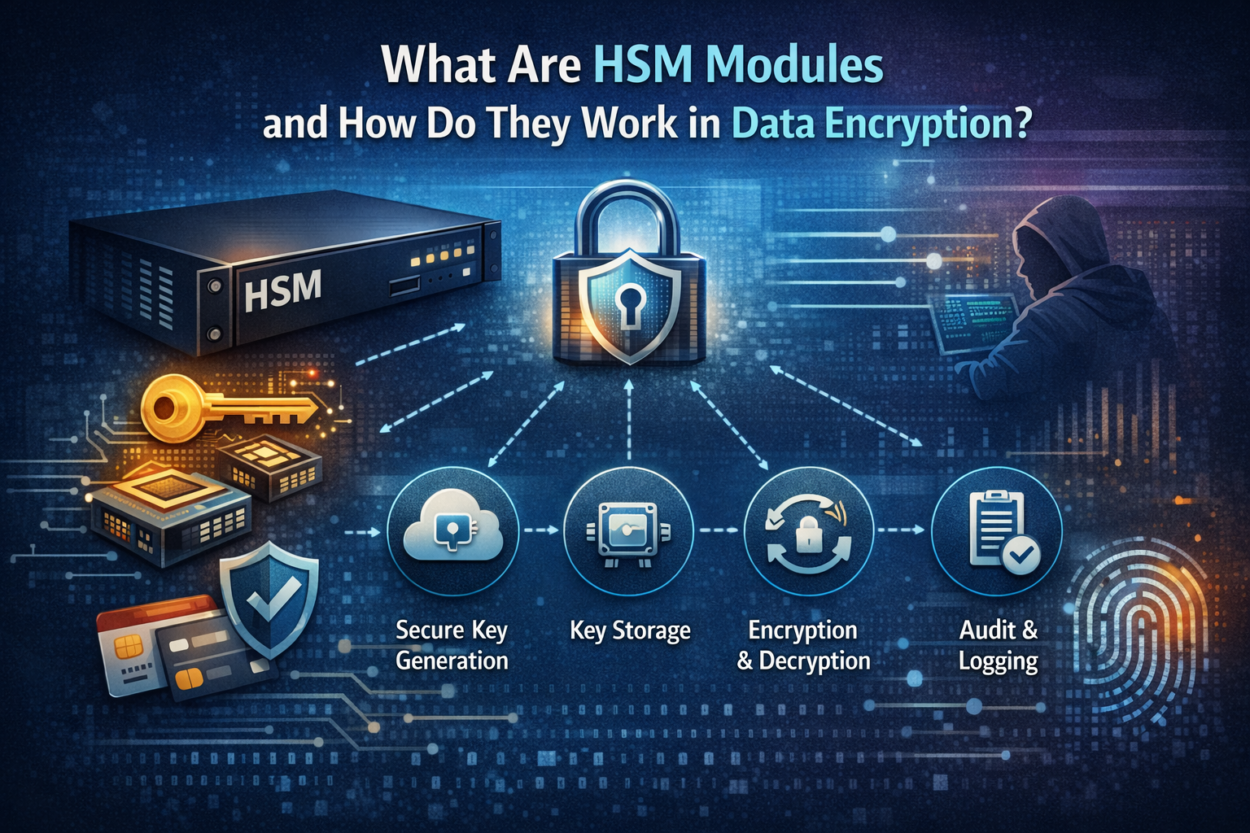
How Do HSM Modules Work?
Understanding how HSM modules work can help businesses see their value more clearly. These devices follow a structured process to handle encryption securely.
1. Secure Key Generation
HSM modules generate encryption keys within the device itself. This ensures that keys are created in a safe environment and are not exposed to external systems.
2. Key Storage
Once the keys are generated, they are stored inside the HSM in an encrypted format. The keys never leave the device in plain text, which prevents unauthorized access.
3. Encryption and Decryption
When data needs to be encrypted or decrypted, the HSM performs these operations internally. The sensitive data is processed securely without exposing the keys.
4. Access Control
HSM modules use strict authentication methods to control access. Only authorized users or systems can perform operations, ensuring complete control over data security.
5. Audit and Logging
All activities performed by the HSM are recorded. This helps businesses monitor usage, detect suspicious activities, and maintain compliance with regulations.
Types of HSM Modules
Different businesses have different security needs. HSM modules are available in various types to meet these requirements.
1. Network HSM
These are connected to a network and can be used by multiple systems. They are ideal for large organizations handling high volumes of transactions.
2. PCIe HSM
These modules are installed directly into servers using PCIe slots. They offer fast performance and are suitable for applications that require quick processing.
3. USB-Based HSM
These are portable HSM devices used for smaller applications. They are easy to deploy and useful for specific tasks like code signing.
4. Cloud HSM
Cloud-based HSM solutions allow businesses to manage encryption keys in a cloud environment. They are flexible and scalable for modern businesses.
Use Cases of HSM Modules
HSM modules are widely used across different industries to secure sensitive data.
Banking and Financial Services
- Secure payment processing
- PIN generation and verification
- Protect cardholder data
Healthcare
- Protect patient records
- Secure medical data exchange
E-commerce
- Protect customer data
- Secure online transactions
Government and Defense
- Protect classified information
- Ensure secure communication
IT and Cloud Services
- Manage encryption keys
- Secure cloud infrastructure
Role of HSM Modules in Payment Security
HSM modules play a crucial role in securing digital payments. They are used to protect transaction data and ensure that sensitive information is not exposed.
In payment systems, HSM modules help in:
- Encrypting transaction data
- Managing PIN security
- Preventing fraud and unauthorized access
This is why payment HSM solutions are widely used by banks and fintech companies.
How to Choose the Right HSM Module
Choosing the right HSM module is important for achieving the best security results. Businesses should consider the following factors:
- Security certifications and compliance support
- Performance and scalability
- Integration with existing systems
- Ease of management
- Vendor support and reliability
Selecting the right solution ensures that your data remains protected without affecting system performance.
Future of HSM Modules in Data Security
As technology continues to grow, the role of HSM modules will become even more important. Businesses are moving toward advanced encryption methods, and HSM modules will support these developments.
Future trends include:
- Increased adoption of cloud HSM
- Integration with IoT security systems
- Support for blockchain technologies
- Enhanced automation in key management
Organizations that invest in HSM modules today will be better prepared for future security challenges.
Conclusion
Data encryption is a critical part of modern business security, and protecting encryption keys is just as important as encrypting data itself. HSM modules provide a secure and reliable way to manage keys and perform cryptographic operations.
With features like tamper resistance, secure key storage, and strong access control, HSM modules help businesses protect their sensitive information and build trust with customers.


Leave a Comment